2020 Identity Proofing Scorecard: Enterprise Solutions
- Date:November 05, 2020
- Author(s):
- Krista Tedder
- Tracy (Kitten) Goldberg
- Report Details: 26 pages, 17 graphics
- Research Topic(s):
- Fraud & Security
- Fraud Management
- PAID CONTENT
Overview
Mitigation of Identity fraud requires a combination of technologies that are complementary and easy to manage. Adding a new technology solution requires an approach that looks beyond fraud management to the customer experience in all stages of the customer life cycle. Not only is it critical to have a safe and secure onboarding experience, but identity management also needs to enable access and step-up authentication and bind the identity to the account, all while preventing account takeover and new-account fraud.
This report reviews and ranks technology providers that offer enterprise-wide identity-proofing solutions. Javelin evaluated 26 technology providers and created a ranking of the enterprise providers.
Key questions discussed in this report:
- What technologies are available that provide protection against account takeover and new-account fraud?
- What capabilities are available to fraud operations units to manage identity-proofing technologies?
- Is the industry prepared for the change in how digital fraud is occurring?
Methodology
Requests for information using three classifications of product components were used (product vitals, features, and administration). The email requests were sent to vendors on June 23, 2020, with responses due back to Javelin by July 17, 2020. Based on the vendor responses and the data provided, product demonstrations were reviewed by Javelin through Aug. 21, 2020. All rankings and analyses were completed by Sept. 25, 2020.
Screenshots, videos, written responses, website collateral, and interview responses were used as a foundation to rank the vendors.
Javelin created a methodology to identify the point totals, which ranged from API integrations from other companies to full-feature maturation.
Product vitals: 37 elements scored
Product features: 39 elements scored
Administration: 14 elements scored
Each element could have scored up to 100 point
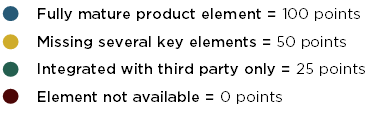
The highest score possible was 300.
Book a Meeting with the Author
Related content
2026 Direct-to-Consumer Identity Protection Services Overview: Gains, Gaps, and Opportunities for Industry Growth
Javelin Strategy & Research’s biennial assessment of direct-to-consumer identity theft protection services (IDPS) vendors finds that they are expanding their services. They are off...
Money Mules: The Fraud-Laundering Connection
Money mules are no longer just a money laundering problem. They now sit at the center of scams, identity fraud, payment fraud, and organized financial crime, helping criminals move...
2026 U.S. Identity Protection Services Market Report: U.S. Market Poised to Hit $18 Billion by 2027
The U.S. identity theft protection services (IDPS) market is forecast to hit $18 billion by the end of 2027, as consumer investment in identity theft protection continues to grow. ...
Make informed decisions in a digital financial world