2021 Identity Fraud Study: Shifting Angles
- Date:March 23, 2021
- Author(s):
- John Buzzard
- Tracy (Kitten) Goldberg
- Report Details: 54 pages, 31 graphics
- Research Topic(s):
- Fraud & Security
- Fraud Management
- PAID CONTENT
Overview
Javelin’s 2021 Identity Fraud Study provides a comprehensive analysis of fraud trends in the context of a changing technological and payments landscape to inform consumers, financial institutions, and businesses about the most effective means for controlling identity fraud. The study began in 2003, and serves as the nation’s longest-running analysis of identity fraud, with over 90,000 consumers surveyed.
This study is independently produced by Javelin Strategy & Research and made possible with support from the following sponsors:
 | |||||||
 |  |  | |||||
Interested in sponsoring a future study?
PERMISSIONS AND COPYRIGHT GUIDELINES
Only Platinum sponsors of this study are granted rights to use figures and data from the 2021 Identity Fraud Study in their marketing campaigns and external communications.
This report is copyrighted and may not be distributed. Javelin’s Advisory Services clients do not have rights to cite any findings in their marketing campaigns, press releases, webinars, or any other external communications.
Javelin retains the ownership of the report, survey, raw data, methodology and all other project deliverables. While Javelin may grant other non-competing organizations rights to use the project’s findings in other public venues, we retain ultimate discretion over such decisions.
OVERVIEW
Since 2003, Javelin has researched the annual nuances of identity fraud. Identity fraud has quickly transformed through unique societal changes related to innovation, the COVID-19 pandemic, and criminal tactics that focus on corporate and consumer targets. As total identity fraud losses climbed to $56 billion (USD) in 2020, it is important to make some distinctions between the two emerging types of attack vectors that criminals used in 2020 to perpetrate identity fraud.
Javelin has relied solely on the term identity fraud, without the need for further distinctions. As criminals focus intently on consumers as the path of least resistance in their quest to steal personal information, their tactics have changed. The routine theft and usage of consumers’ personally identifiable information (PII) for criminal profit is still regarded by Javelin as traditional identity fraud. When it comes to traditional identity fraud, consumers have a scant perspective on the exact time and technique used by criminals to steal their information. They simply understand that a loss of PII occurred, resulting in financial damage that they must resolve.
Identity Fraud Tactics Diverge
Figure 1. How Identity Fraud Has Shifted
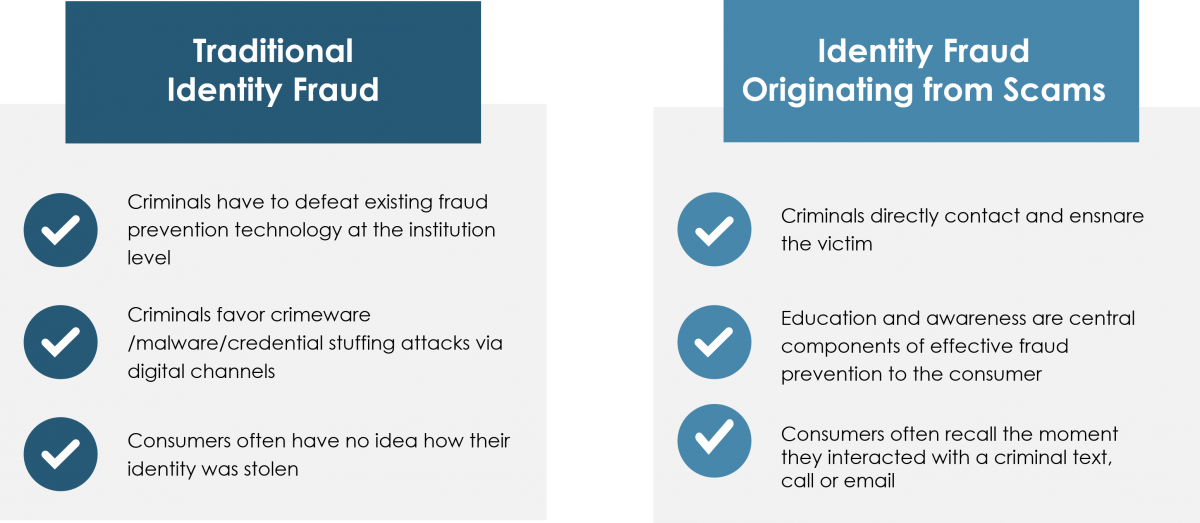
Source: Javelin Strategy & Research, 2021
A new and significant identity fraud threat was identity fraud scams that resulted in $43 billion (USD) in losses to US consumers. Identity fraud scams are relatively easy to orchestrate and present an opportunity for criminals to bypass the fraud-detection barriers maintained by financial services providers, because they directly target the consumer. The consumer, within the context of identity fraud scams, becomes the path of least resistance. Access to the treasure chest of PII that enables criminals to take over consumers’ identities now becomes more tangible, because consumers continue to be vulnerable targets. A noteworthy characteristic of identity fraud scams is that consumers often recall the moment they interacted with a criminal through a text, call, or email.
Methodology
In 2020, Javelin conducted a nationally representative online survey of 5,000 U.S. consumers to assess the impact of fraud, uncover where fraudsters are making progress, explore consumers’ actions and behaviors and how it relates to fraud risk levels, and identify segments of consumers most affected by fraud.
Book a Meeting with the Author
Related content
2026 U.S. Identity Protection Services Market Report: U.S. Market Poised to Hit $18 Billion by 2027
The U.S. identity theft protection services (IDPS) market is forecast to hit $18 billion by the end of 2027, as consumer investment in identity theft protection continues to grow. ...
2026 Identity Fraud Study: The Illusion of Progress
The Javelin Strategy & Research 2026 Identity Fraud Study provides a comprehensive analysis of fraud trends amid a changing landscape for technology and payments. Its goal is to in...
Iran Cyber Risk: ‘Five-Alarm Fire’ for U.S. Banks, Critical Infrastructure
Iran-linked cyber activity is no longer hypothetical for U.S. financial institutions. International tensions, collaboration by adversaries, and gaps in oversight are reshaping fina...
Make informed decisions in a digital financial world
